Wpisy na Blogu
Szczegółowe omówienia odkrytych przez nas podatności, innowacyjnych technik testów bezpieczeństwa i praktycznych spostrzeżeń z badań nad ochroną dużych organizacji.

How to Choose a Penetration Testing Company - The 2026 Buyer's Checklist
A five-stage checklist for evaluating and choosing a penetration testing company - scope qualification, vendor vetting, proposal scoring and report anatomy.
Buyer's Guide

Paweł Woyke
May 7, 2026
9
min read
•
May 7, 2026

Time of Check Time of Use (TOCTOU): Anatomy of a Race Condition in GNU sed
CVE-2026-5958 is a textbook TOCTOU bug that sat inside GNU sed's --follow-symlinks path for two decades. This post walks through the race at the syscall level and the fix shipped in sed 4.10.
Vulnerability research

Marcin Wyczechowski

Michał Majchrowicz
May 1, 2026
9
min read
•
Apr 24, 2026
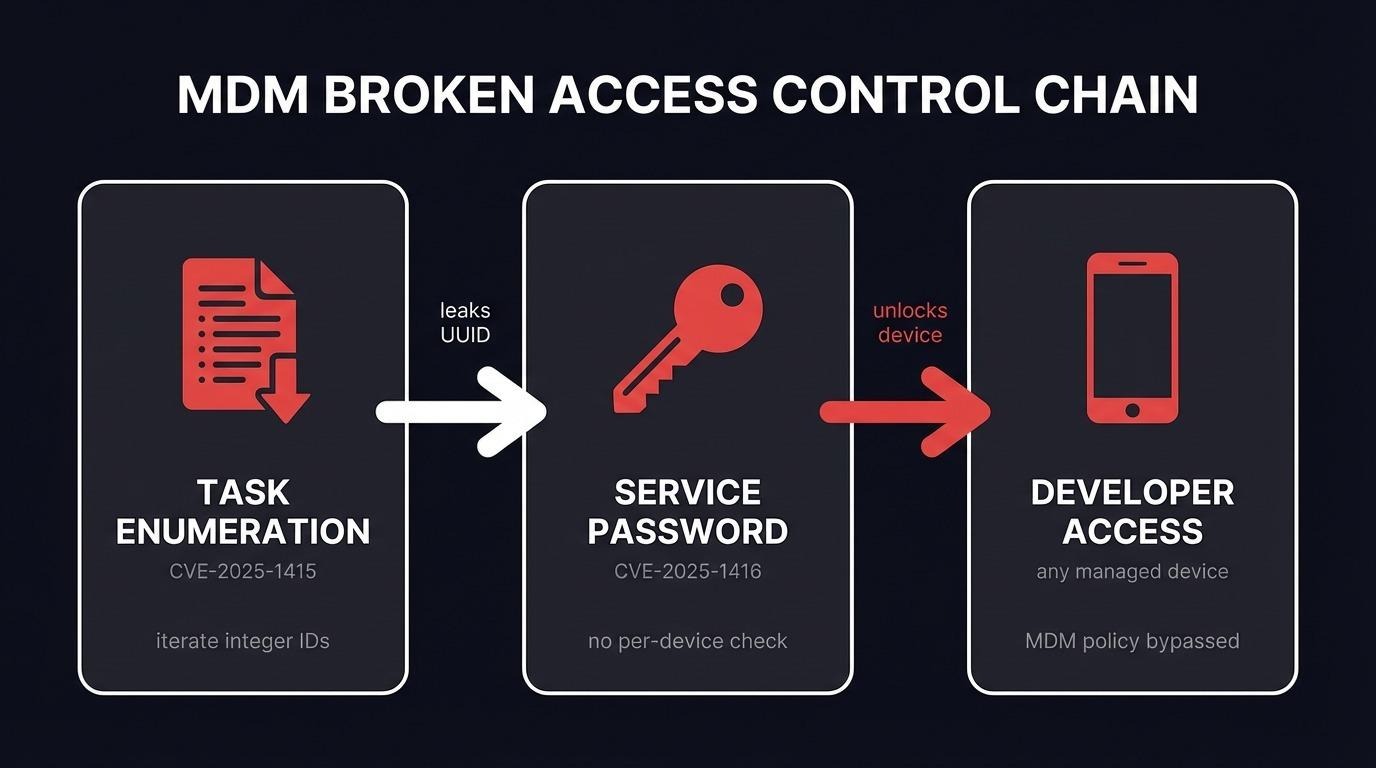
Broken Access Control in the Real World: Chaining Two Bugs to Extract MDM Service Passwords
A low-privileged user with no UI permissions chained two broken access control bugs in an MDM REST API to extract service passwords for every managed device. Full walkthrough of CVE-2025-1415 and CVE-2025-1416, from task enumeration to full developer access on any phone in the fleet.
Vulnerability research
API

Marcin Węgłowski
April 24, 2026
10
min read
•
Apr 21, 2026

Attacking MLflow: How ML Artifacts Become Attack Vectors
Two vulnerabilities in MLflow found during source code audit. Stored XSS via unsafe YAML parsing (CVE-2026-33865) and authorization bypass on artifact downloads (CVE-2026-33866). Both patched.
Vulnerability research

Sławomir Zakrzewski
April 9, 2026
9
min read
•
Apr 9, 2026
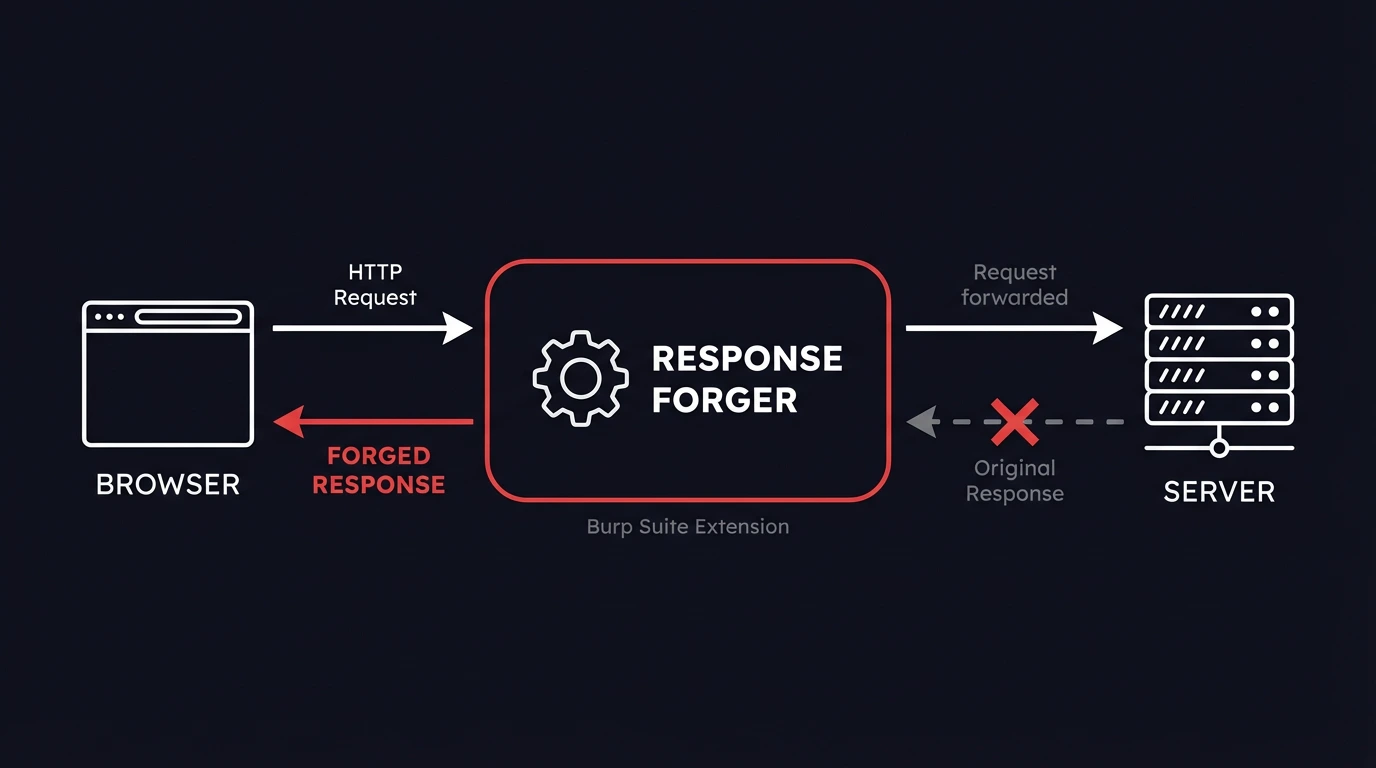
Response Forger - A Burp Suite Extension to Modify Responses on the Fly
Every pentester hits the same wall - Burp Suite's Match and Replace swaps fragments, but it can't override an entire HTTP response. Response Forger fixes that. Define a URL pattern, paste the full response you want the browser to receive, done.
Web

Marcin Węgłowski
April 7, 2026
9
min read
•
Apr 7, 2026
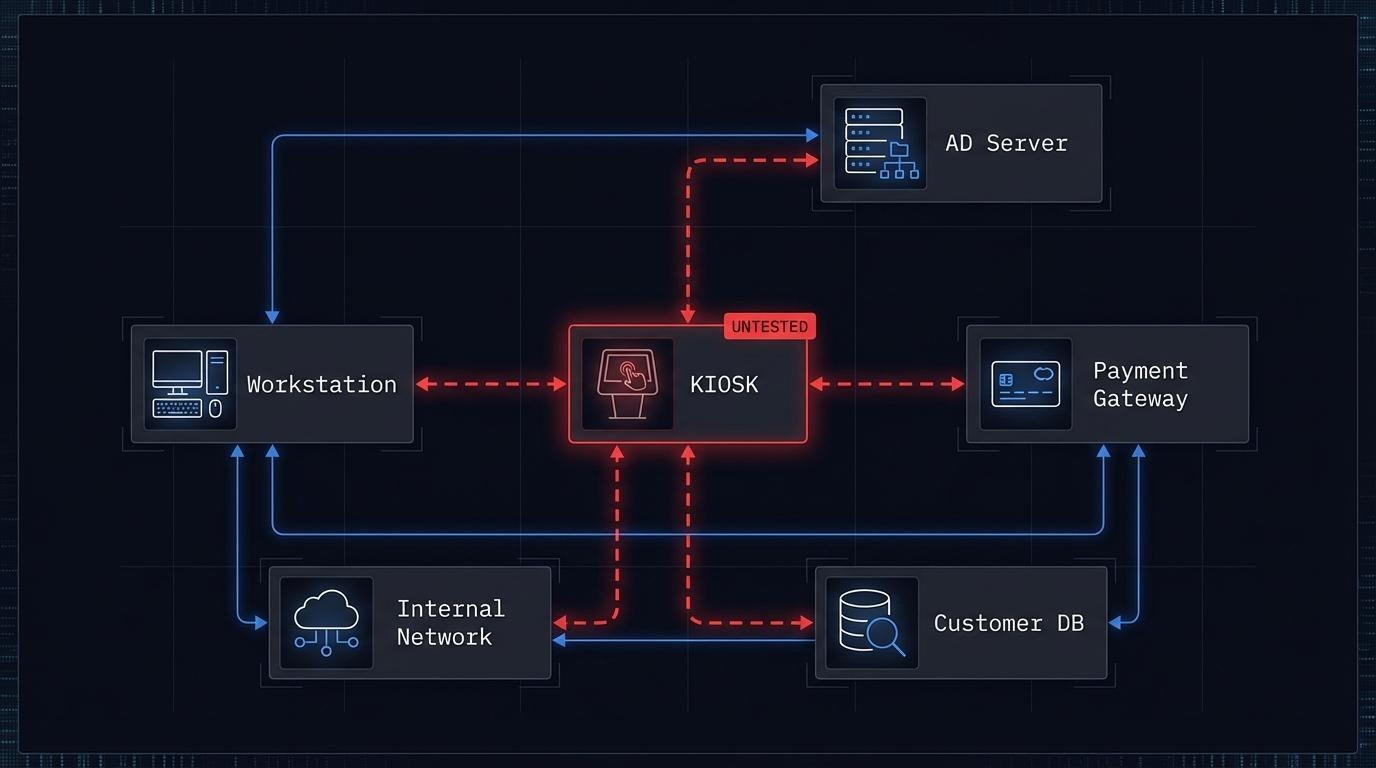
Kiosk Security: Why Self-Service Terminals Are the Weakest Link in Your Network
Kiosks process payments, collect personal data, and sit on corporate networks - but almost never appear in pentest scopes. This post breaks down real kiosk compromises, the compliance frameworks that require testing, and what a kiosk penetration test actually covers.
Hardware

Maksymilian Kubiak
April 21, 2026
9
min read
•
Apr 2, 2026
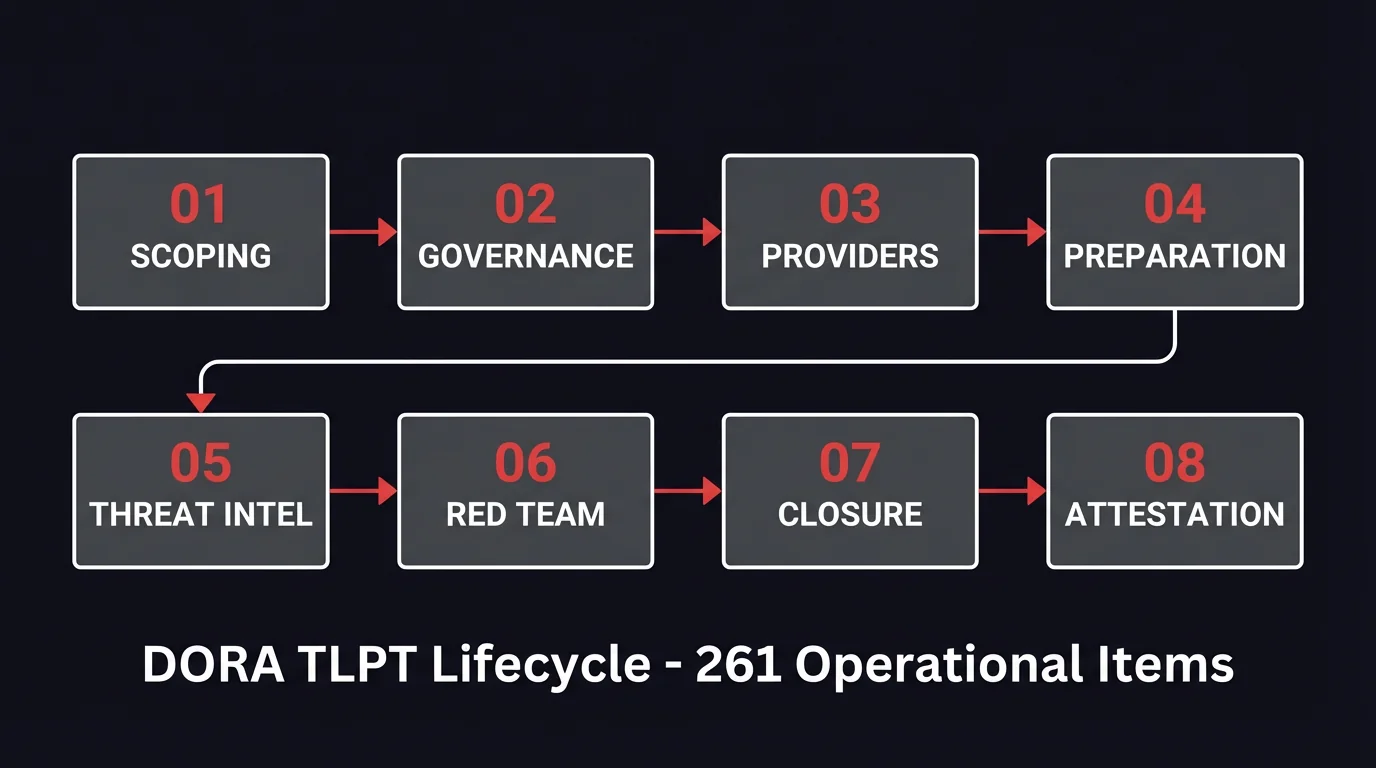
Checklista TLPT DORA: 261 kroków do zgodności
Checklista TLPT DORA z 261 punktami operacyjnymi w 8 fazach cyklu. Każdy z odniesieniem do konkretnego artykułu RTS. Karty oceny dostawców, rejestr ryzyk, porównanie 32 jurysdykcji.
Buyer's Guide

Paweł Woyke
May 6, 2026
10
min read
•
Mar 30, 2026
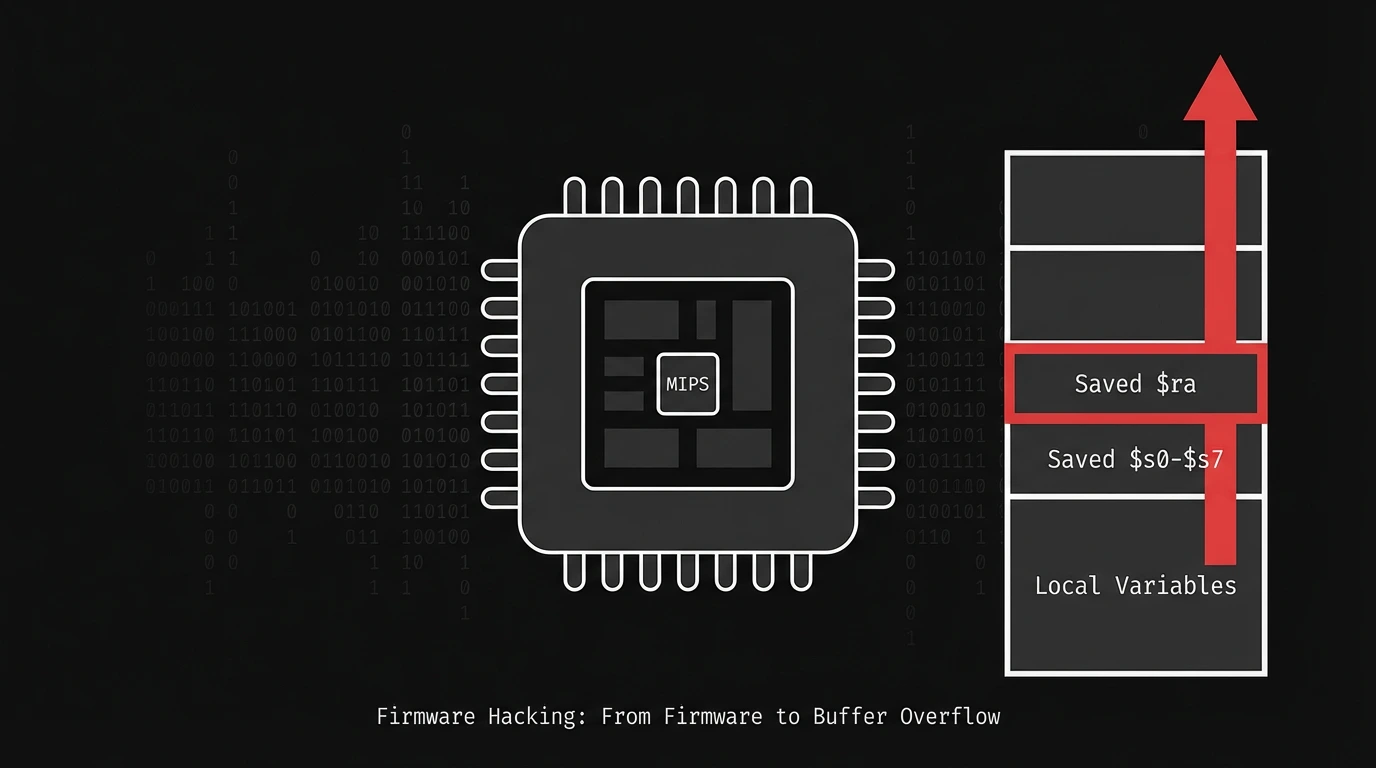
Firmware Hacking: From Router Firmware to Buffer Overflow on MIPS
Full pipeline walkthrough: firmware extraction, Ghidra reverse engineering, QEMU emulation, and GDB fork-following to confirm a pre-auth stack buffer overflow in a MIPS router CGI binary. Including the debugging and troubleshooting steps most writeups skip.
Hardware

Franciszek Malek
April 7, 2026
19
min read
•
Mar 27, 2026
TLPT DORA 2026: Wymogi RTS i 6-Fazowy Proces Testowania
Kompletny przewodnik po TLPT pod DORA - kto jest objęty obowiązkiem, jak przebiega każda z sześciu faz, czego wymaga regulacja od red teamów i dostawców threat intelligence, i na co zwrócić uwagę przy wyborze partnera.
Buyer's Guide

Paweł Woyke
April 3, 2026
14
min read
•
Feb 24, 2026
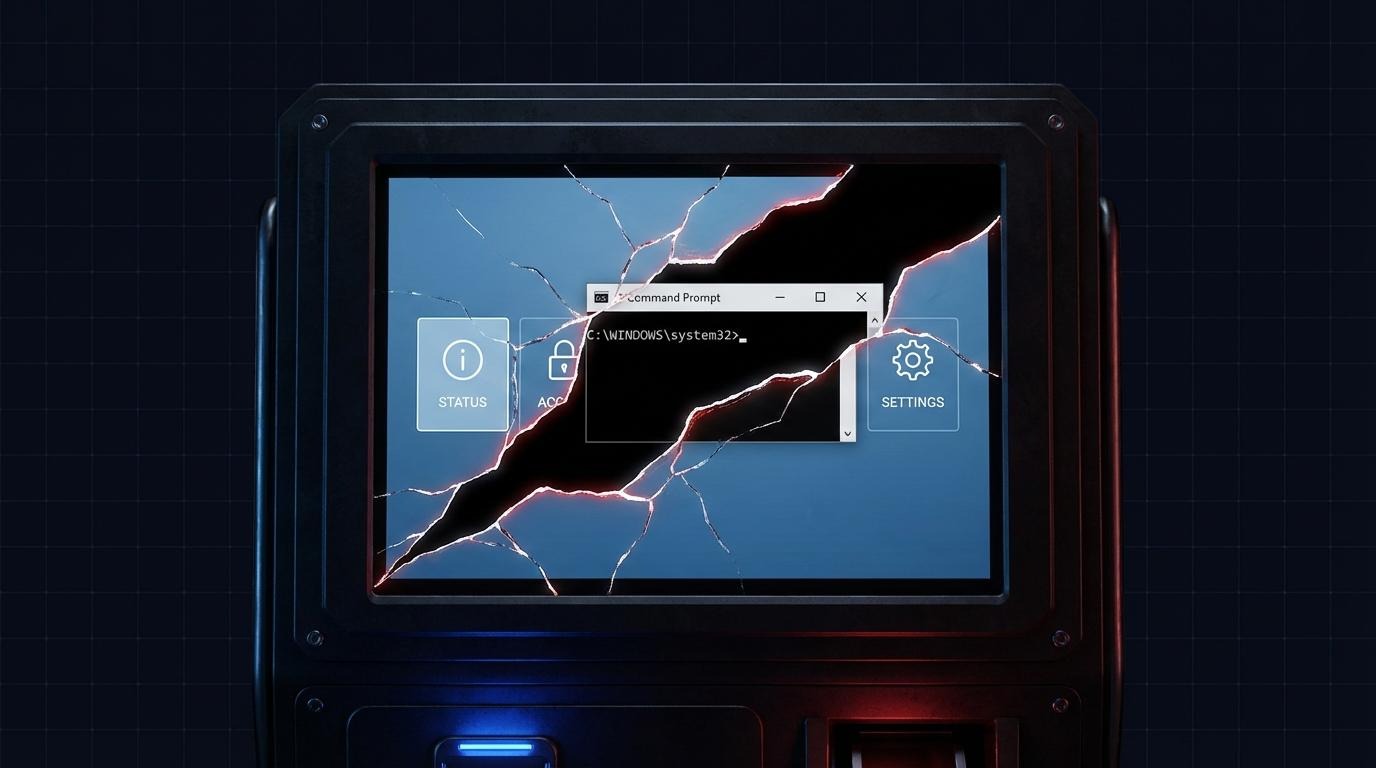
Kiosk Breakout: From PIN Bypass to NT AUTHORITY\SYSTEM
Three kiosk breakout techniques chained during an AFINE engagement - from cracking a KioWare PIN to NT AUTHORITY\SYSTEM. Covers CVE-2024-3459, CVE-2024-3460, and a bypass of CVE-2022-44875 across file dialog escapes, Adobe Acrobat sandbox escape, and iframe privilege escalation.
Vulnerability research
Windows

Maksymilian Kubiak
March 27, 2026
12
min read
•
Mar 25, 2026
Next
1 / 7
Sort by Categories
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
Miesięczny Raport Ofensywny
Dołącz do naszego newslettera! Co miesiąc ujawniamy nowe zagrożenia w oprogramowaniu biznesowym, wskazujemy kluczowe luki wymagające uwagi oraz analizujemy trendy w cyberbezpieczeństwie na podstawie naszych testów ofensywnych.
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
Cookie Settings
We use cookies to provide you with the best possible experience. They also allow us to analyze user behavior in order to constantly improve the website for you.
See our Privacy PolicyThank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
