We created a practical DORA compliance checklist based on 10 years of offensive security experience. It covers the full DORA RTS on threat-led penetration testing - all 16 articles, 8 annexes - and cross-referenced it against DORA Articles 26-27, the TIBER-EU 2025 framework, and 32 national implementation guides.
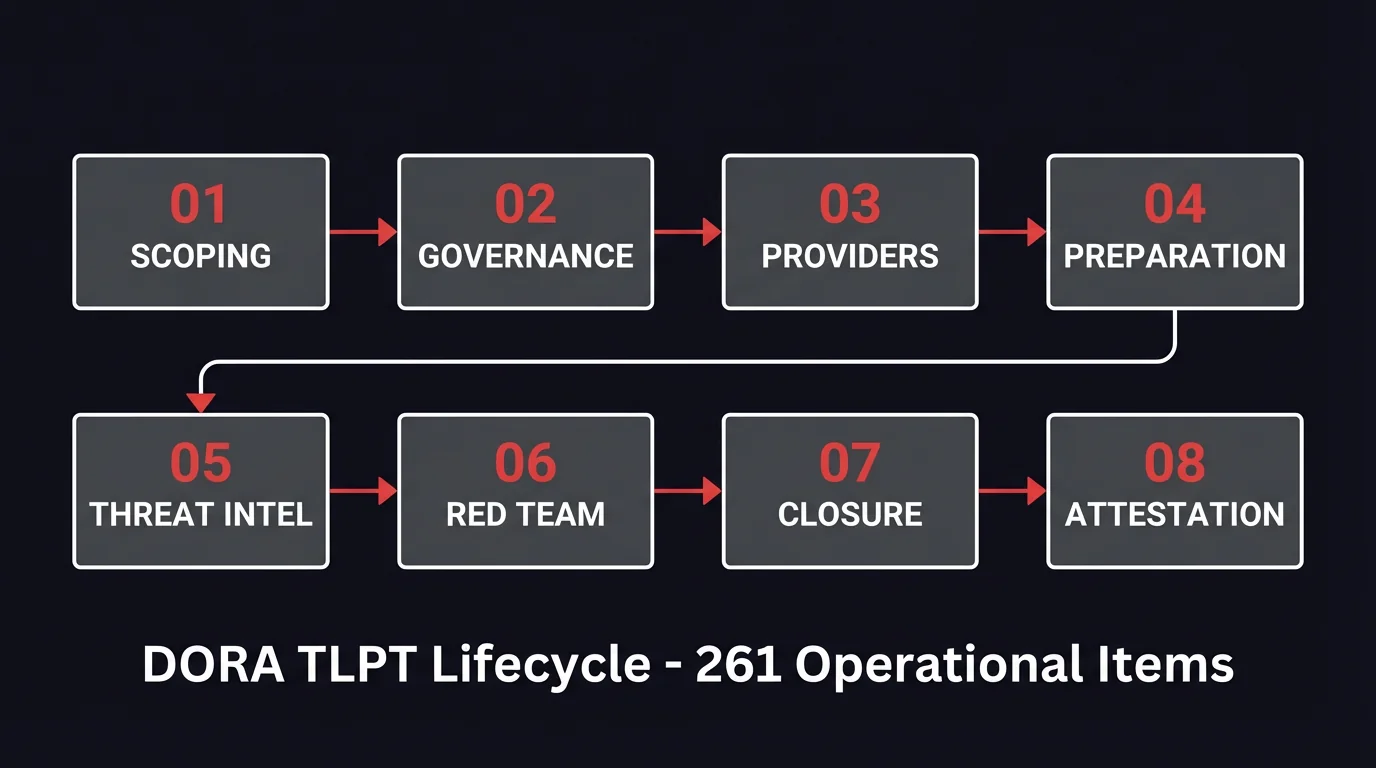
This DORA compliance checklist has 261 operational items across 8 phases of the TLPT lifecycle. Every item traces back to a specific RTS article or TIBER-EU reference. The item tells you what to do, which article requires it, and what the gate is before you move to the next phase.
What's in the checklist beyond the 261 items:
- Provider evaluation scorecards - 14 weighted criteria for TI providers (max 175 points), 17 for red team (max 210). Scoring thresholds tell you when a provider meets the bar and when they don't.
- Pre-populated risk register - the 10 risks that derail TLPTs, with likelihood and impact scoring already filled in
- 32-jurisdiction comparison table - which jurisdictions have a TLPT authority, which allow internal testers, where the RTS gets extra requirements layered on top
- 23 Red Team Insights - practitioner tips from the offensive security side. What makes the difference between an institution that's ready and one that isn't.
- Interactive Excel - plug in your notification date and the timelines calculate themselves. Progress dashboards track completion across all 8 modules.
The free download with interactive PDF and Excel are below.
The DORA TLPT requirement in practice
If you've only skimmed Articles 26 and 27, here's what the DORA threat-led penetration testing requirements look like once you unpack the RTS: a mandatory exercise every 3 years, with at least 12 weeks of active red team testing. You need an external threat intelligence provider - the RTS doesn't let you skip that. Purple teaming moved from "recommended" under older TIBER frameworks to mandatory. And if you've used the same red team provider twice, expect your regulator to ask questions about rotation.
That's just the EU-level baseline. Each member state designates its own TLPT authority and can add requirements on top. As of March 2026, 20 countries have published national TIBER guides with their own specifics. The other 12 are applying the RTS directly without a published national document - which creates its own kind of ambiguity. The checklist's 32-jurisdiction comparison table maps all of this so you're not piecing it together from 30 different regulator websites.
Where institutions get stuck - three operational bottlenecks
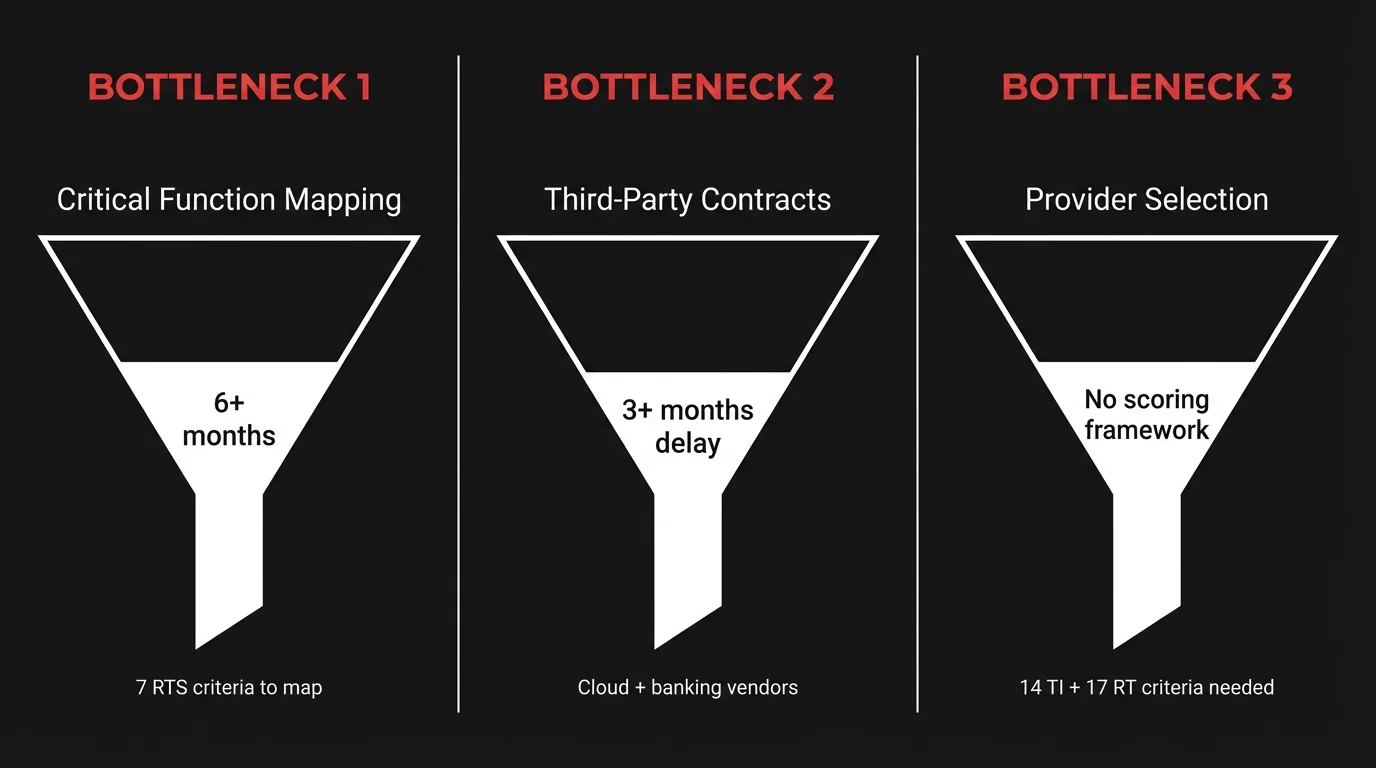
These are the three areas where preparation falls apart most often - and where the checklist goes deepest.
Critical function mapping
Before anyone writes a test plan, someone at the institution needs to answer: which business processes run on which ICT systems, and which of those are critical enough to fall in scope? RTS Article 9(7) lists 7 criteria for ranking critical functions - criticality to the sector, business relevance, substitutability, interconnectedness, geographical location, sectoral dependence, and available threat intelligence.
Most banks don't have this mapping. Not in a usable form. The information exists across architecture diagrams, CMDB exports, and the heads of three people who've been in the company the longest. Pulling it together into something that satisfies a regulator consumes the entire 6-month scoping window when started from scratch.
The checklist structures this against the 7 RTS criteria so you can start before notification arrives. Start this 6+ months early.
Third-party provider coordination
DORA Article 30(3) requires cooperation clauses in contracts with ICT third-party providers that fall in TLPT scope. In practice, that means getting your cloud provider or core banking vendor to sign an amendment saying they'll cooperate with a red team exercise against their infrastructure.
Their legal team will have questions. Their risk team will have objections. Their timeline will not match yours. A single contract amendment can delay TLPTs by 3+ months. Module 04 of the checklist covers this with 14 items - contract amendments, data handling agreements, and cross-border arrangements.
Provider selection without evaluation criteria
RTS Article 7(1) sets minimum requirements for TI and red team providers - experience, certifications, insurance, references. But it gives you no way to score one provider against another. Most procurement departments end up comparing proposals on price because they have no other framework.
The checklist includes weighted evaluation scorecards: 14 criteria for TI providers (max 175 points) and 17 for red team providers (max 210). Each criterion maps to a specific RTS requirement or TIBER-EU procurement guidance item.
One thing worth knowing about certifications: OSCE, OSED, OSEP, OSWE, and CRTO test whether a team can do advanced red team work - lateral movement, custom exploit development, EDR evasion - not just run a vulnerability scanner and write up the output. CVE publications tell you something different: that the provider is finding real vulnerabilities in production software, not just testing for known ones.
What is in the TLPT DORA checklist - phase by phase
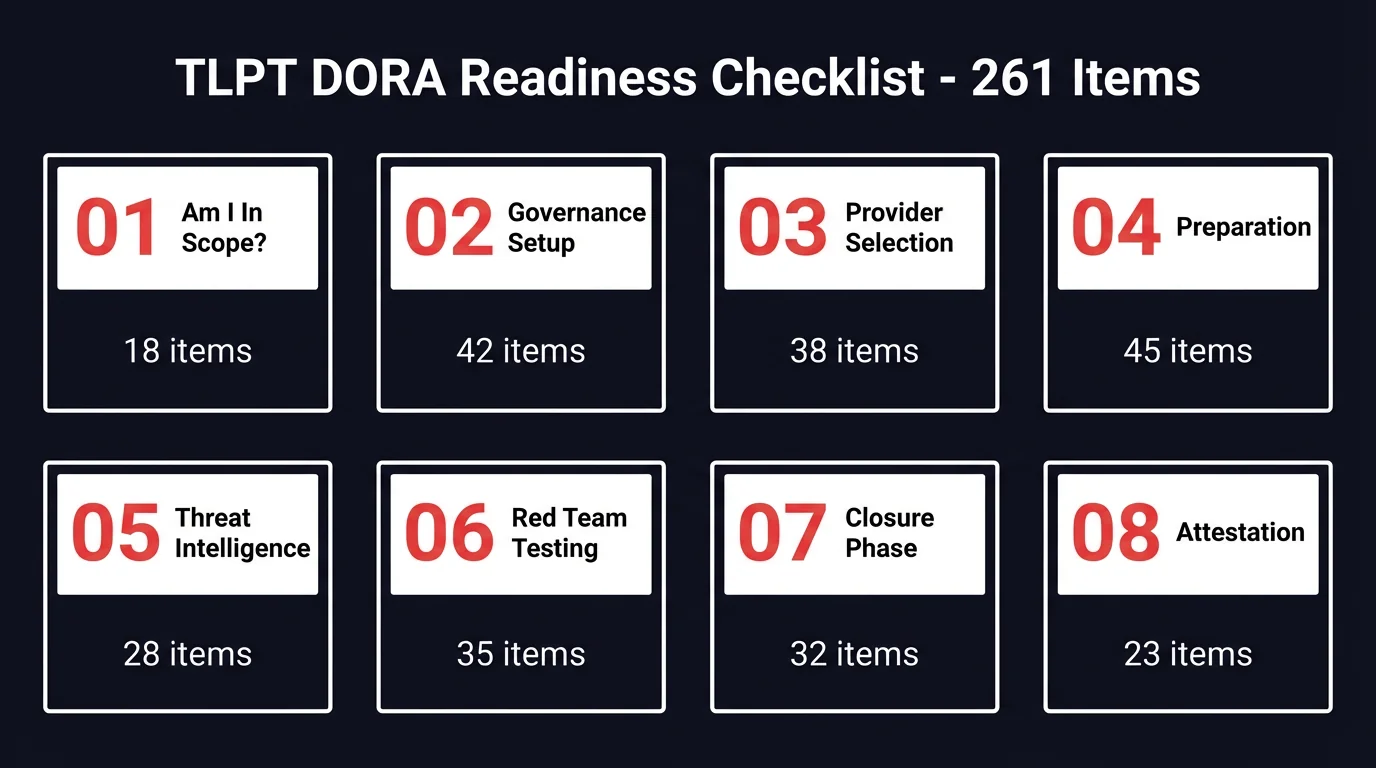
Eight modules, each matching a phase in the RTS. Every item has an article reference so you know exactly why it's there.
Module 01: Am I In Scope? Covers DORA Article 26 thresholds, discretionary designation by national authorities, and exemption criteria. 18 items. Milestone: scope determination completed before formal notification arrives.
Module 02: Governance Setup. Control team formation, secrecy protocols, critical function mapping against the 7 RTS Article 9(7) criteria. 42 items. Milestone: control team lead appointed, CIFs mapped to underlying ICT systems.
Module 03: Provider Selection. Threat intelligence and red team minimum requirements per RTS Article 7, weighted evaluation scorecards, contracting essentials including kill-switch clauses and data handling agreements. 38 items. Milestone: providers contracted with separation of teams confirmed.
Module 04: Preparation Phase. Project charter content (Annex I), scope specification document (Annex II), third-party ICT provider coordination, cross-border mutual recognition arrangements. 45 items. Milestone: TLPT authority approves the scope specification.
Module 05: Threat Intelligence. Intelligence gathering, threat actor profiling, scenario development (minimum 3 scenarios, maximum 1 non-threat-led), and the Targeted Threat Intelligence Report (Annex III). 28 items. Milestone: TLPT authority approves the TTIR.
Module 06: Red Team Testing. Red team test plan (Annex IV), the 12-week minimum active testing period per RTS Article 11(5), leg-up processes, detection management, and weekly reporting. 35 items. Milestone: active testing complete, all actions logged.
Module 07: Closure Phase. Blue team notification, red team report (Annex V, 4-week deadline), blue team report (Annex VI, 10-week deadline), mandatory purple teaming exercise, and test summary report (Annex VII). 32 items. Milestone: test summary submitted to TLPT authority.
Module 08: Remediation and Attestation. Remediation plan with root cause analysis (8-week deadline per RTS Article 13), formal attestation per RTS Article 14(1) (Annex VIII). 23 items. Milestone: attestation issued.
A note on Module 07: purple teaming is not a debrief with slides. The RTS makes it mandatory, but the format is up to you - and the difference between a useful session and a wasted one is enormous. The best purple teaming we've seen has the blue team sitting with the red team, replaying attack paths in real time, tuning detection rules on the spot, validating fixes before the session ends. If your plan is a two-hour meeting with a PowerPoint, you're leaving 80% of the value on the table.
What else is in the DORA checklist
Beyond the 261 items, the checklist includes tools you'd otherwise build from scratch - or more likely, skip and regret later.
Provider evaluation scorecards. 14 weighted criteria for TI providers (max 175 points), 17 for red team (max 210). Mapped to RTS Article 7 and TIBER-EU procurement guidance. Scoring thresholds tell you when a provider meets the bar - useful when procurement asks why the cheapest bidder isn't good enough.
Pre-populated risk register. The 10 risks that show up during TLPTs - data exposure, production system disruption, detection management failures, provider coordination breakdowns. Likelihood and impact scoring already filled in. Adjust to your context instead of starting from a blank template.
32-jurisdiction comparison table. Every EU/EEA country plus the UK. TLPT authority name, framework status, internal tester rules, key differences from the RTS. If you operate across borders, this saves weeks of research across regulator websites. Current as of March 2026.
23 Red Team Insights. The practitioner tips are the part we're most proud of. They come from the offensive security side - what makes the difference between an institution that's ready for testing and one that isn't. Where tests stall, what causes scope creep, how to handle leg-ups without invalidating results.
Interactive Excel. Plug in your expected notification date. The timelines calculate themselves. Progress dashboards track completion across all 8 modules, and conditional formatting flags anything overdue.
Who this checklist is for
- Control team leads managing the TLPT process internally - the day-to-day operational owners of a 12 to 18-month exercise
- CISOs reporting to the management body on TLPT readiness and budget allocation (ty
- Compliance and risk teams verifying regulatory alignment against the RTS and mapping gaps before the TLPT authority notification
- Procurement teams evaluating TI and red team providers using the weighted scorecards instead of ad hoc criteria
Download the TLPT DORA Checklist

Both formats contain the full 261-item checklist, provider scorecards, risk register, country comparison table, and all 23 Red Team Insights.
Direct download. No form required.
Book a TLPT consultation
If you're preparing for TLPT and want to talk through your specific situation, book a consultation. We specialize in offensive security - 150+ CVEs published across SAP, Microsoft, IBM, CyberArk, F5, Palo Alto Networks, and others. We work with banks, financial institutions, and regulated entities across Europe, Asia, and the US.
Book a 30-minute TLPT consultation
Frequently Asked Questions
Who is required to conduct TLPT under DORA?
The short answer: RTS Article 2 sets the thresholds - G-SII and O-SII credit institutions, payment institutions above EUR 150 billion in transaction volume, CSDs, CCPs, and insurance undertakings above EUR 1.5 billion in gross written premiums. But national authorities can also designate entities at their discretion based on systemic importance or ICT risk profile (DORA Article 26(8)). If you're not sure whether you're in scope, Module 01 of the checklist walks through the criteria.
How long does a TLPT take?
Longer than most people expect. 12 to 18 months for the full lifecycle - preparation, testing, closure, remediation. The active red team testing alone takes a minimum of 12 weeks (RTS Article 11(5)). Then add the closure phase: red team report due within 4 weeks, blue team report within 10 weeks, mandatory purple teaming, and an 8-week deadline for the remediation plan. Post-testing activities alone can stretch to 26 weeks.
Can the same company provide threat intelligence and red team testing?
Yes, but with a catch. RTS Article 7(1) requires contractual separation - the TI team and the red team must operate independently with separate staff and no reporting relationship between them. Same company is fine. Same people is not.
Is purple teaming mandatory under TLPT DORA?
Yes. RTS Article 12(5) makes purple teaming mandatory during the closure phase. The blue team and red team must replay offensive and defensive actions on jointly identified topics within 10 weeks of active testing completion. This was not always required under earlier TIBER frameworks.
How often must TLPTs be conducted?
Every 3 years per DORA Article 26(1). Given the 12 to 18-month lifecycle, the math is tight - by the time you finish one TLPT, preparation for the next one is already on the horizon. Module 08 of the checklist includes next-cycle planning for exactly this reason.
Get AFINE's security research and DORA updates directly. No spam, unsubscribe anytime.