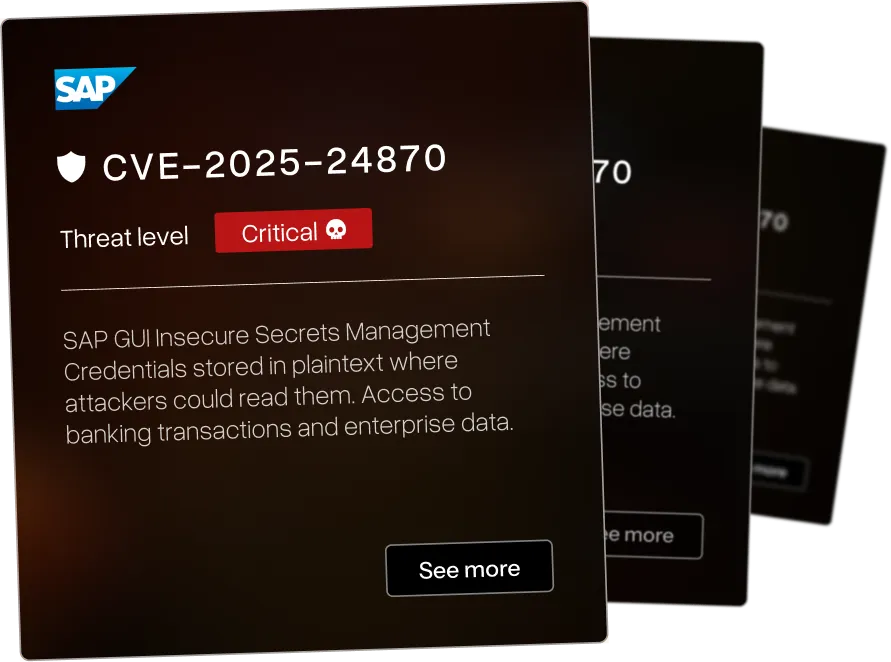
What This Vulnerability Research Portfolio Represents
Discoveries That Matter
Our vulnerability research team reverse engineers your enterprise software to find the 0-days that threaten your infrastructure - before attackers do.

Enterprise Focus
The vulnerabilities below affect systems organizations use: SAP. IBM. Check Point. F5. BMC. Microsoft. Rapid7. Cyberark.

Current Research
We identified a wide range of CVEs across various industries - each of the vulnerabilities have been assigned a threat level ranging from critical to low. We pride ourselves in beating others to identify critical CVEs in large infrastructure for orgasations such as IBM and Microsoft.

URL spoofing in OwnCloud password reset emails allows phishing attacks via manipulated reset links






Cross-site scripting in blog-post creation functionality in Amasty Blog Pro for Magento 2






Cross-site scripting in preview functionality in Amasty Blog Pro for Magento 2




.webp)

Stored cross-site scripting in IBM InfoSphere Information Server allows persistent malicious scripts






Stored cross-site scripting in blog-post creation in Amasty Blog Pro for Magento 2 allows persistent script injection






Stored cross-site scripting in comment functionality in Amasty Blog Pro for Magento 2




.webp)

Cross-site scripting in IBM InfoSphere Information Server allows script injection via crafted input





Server-side remote code execution in Foreman allows authenticated attackers to execute arbitrary commands on the server






Open redirect in OurUmbraco allows attackers to redirect users to malicious external websites






Authenticated stored XSS in Autoptimize WordPress plugin allows administrators to inject persistent scripts






Race condition leading to remote code execution in Autoptimize WordPress plugin allows arbitrary file writes






Arbitrary file upload in Autoptimize WordPress plugin allows uploading and executing malicious PHP files






Security vulnerability in Dell EMC NetWorker allows privilege escalation or unauthorized access






Security vulnerability in Dell EMC NetWorker allows privilege escalation or unauthorized access (second issue)






Windows Print Spooler elevation of privilege (PrintNightmare) - allows remote code execution and local privilege escalation




We map your systems before testing how they break.
That's why critical findings usually show up outside the original scope - attackers don't respect scope documents.
Security Assessment Services FAQ
Questions enterprise security teams ask before partnering with AFINE for security assessments.