Security Assessment Services for Enterprise
Offensive security services for organizations
where a breach means more than headlines.
Tested by researchers with CVEs in SAP, CyberArk, Microsoft, Palo Alto...
Our security assessment team has published 150+ CVEs in enterprise software from major vendors. We understand not just what breaks, but why it breaks and how attackers exploit it.
Trusted by:
PKO BP
ING BANK
Medicover
Bank BPS
Bank BGK
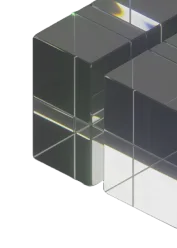
Does Your Security Assessment Match Your System Complexity?
Our security assessment services are
designed around your specific industry challenges:
Does Your Security Assessment Cover Your Actual Attack Surface?
Your security team secures the documented systems.
Your pentests validate the defined scope.
Your actual attack surface?
The gaps between systems.

The integration from three years ago nobody remembers.
Lateral movement paths from low-privilege access to production

API chains that circumvent authentication entirely

We map your systems before testing how they break.
That's why our critical findings consistently appear outside the original scope -attackers exploit what you forgot, not what you documented.
Why Manual Security Assessment Matters
You get manual penetration testing by researchers who've spent years finding vulnerabilities in production systems. We understand not just what breaks, but why and how attackers exploit it.
Our team has published 150+ CVEs in enterprise software using this approach.

The Enterprise Security Software We Hacked
You get security assessments from researchers who've published 150+ CVEs in enterprise software. We know how attackers approach complex systems because we've broken them.


Memory corruption in Microsoft Edge (EdgeHTML) allows remote code execution via crafted web content




.webp)

Remote code execution via insecure deserialization in IBM i Access Client Solutions allows attackers to execute arbitrary code






Missing rate limiting on password change in CyberArk EPM allows brute-force attacks against user accounts




View All CVEs We've Published
.webp)


.webp)
What We Deliver
Security assessment designed for teams who need actionable intelligence. We deliver findings your technical teams can fix and business context your leadership can act on.
We’re ready to deliver next-level security
Why Organizations Trust Us
Security Assessment Services FAQ
Questions enterprise security teams ask before partnering with AFINE for security assessments.