Red Team Engagement
for Healthcare
Red Team Engagement for Healthcare by Security Researchers With 150+ CVEs in SAP, IBM, Microsoft, CyberArk and more...
Red Team Engagement That Tests Your Defenses
Most security programs follow this pattern:
Controls look good on paper.
Your SOC has detection rules.
Network segmentation between IT and OT is documented.
Everyone assumes the defenses work.
We show you what breaks, how it breaks, and what customer data is exposed
We simulate attackers who've breached your perimeter and test if they can access EHR systems, compromise medical devices, or exfiltrate PHI. You see which attack paths work and if your defenses stop them.
Why Healthcare Organizations Choose AFINE for Red Team Engagement
We've conducted red team operations on healthcare infrastructure in production for 10 years. You get operators who know how adversaries move from initial compromise to EHR systems and medical device networks, and reports showing exactly which controls failed.

Purple Team Mode Available
Most healthcare clients choose purple team collaboration during red team engagement. Your SOC sees our activity in real time. We explain what we're doing, what it looks like in logs, and how detection should work.
You get both security validation and immediate SOC improvements. Your analysts learn what sophisticated attacks look like while they're happening.
Our Services
What We Cover in Red Team Engagement for Healthcare
Electronic Health Record (EHR) System Access
We test lateral movement from internet-facing systems to EHR infrastructure during red team engagement. Clinical network segmentation effectiveness. Privilege escalation routes. Patient database access controls. We map attack paths from compromised workstations to Epic, Cerner, or Meditech systems and clinical data repositories.
Medical Device Networks and IoMT
We test attack paths to medical device networks and IoMT ecosystems. Infusion pump network access. Patient monitoring system exploitation. PACS workstation compromise. Testing wireless medical device security and whether your SOC detects unauthorized access to life-safety equipment before patient impact.
Patient Portals and Telehealth Platforms
We simulate account takeover and session hijacking attacks on patient-facing systems. API abuse bypassing authorization. PHI extraction through mobile health apps. Testing if fraud detection stops sophisticated attacks on patient authentication and telehealth session security.
Revenue Cycle and Administrative Systems
We test access paths to billing systems, insurance claim processing, and practice management platforms. Testing if compromising administrative systems leads to PHI access or provides pivot points to clinical networks.
SOC Detection and Response
We test if your SOC detects sophisticated attacks on healthcare infrastructure through red team engagement. Do SIEM rules fire on lateral movement to EHR systems? Does EDR catch credential dumping on clinical workstations? Purple team mode provides real-time feedback on detection capabilities for healthcare-specific threats.
Third-Party Integration Security
We assess Health Information Exchange connections, biomedical engineering vendor access, and cloud service provider integrations. Authorization across HL7 and FHIR interfaces. Whether compromise at one integration point provides access to clinical systems and whether monitoring covers third-party activity from HVAC contractors to IT support vendors.
Insider Threat Simulation
We test what happens when legitimate access gets abused - clinical staff credentials compromised, PHI exfiltrated from authorized systems, biomedical engineering access to medical devices. Testing if your monitoring catches insider threats that look like normal clinical workflow behavior.
AI/ML Security Testing
We test AI systems healthcare organizations deploy—prompt injection on clinical chatbots, clinical decision support system manipulation, diagnostic AI model poisoning. PHI extraction from model outputs. Testing if guardrails prevent unauthorized access to training data or manipulation of predictive analytics affecting patient care.
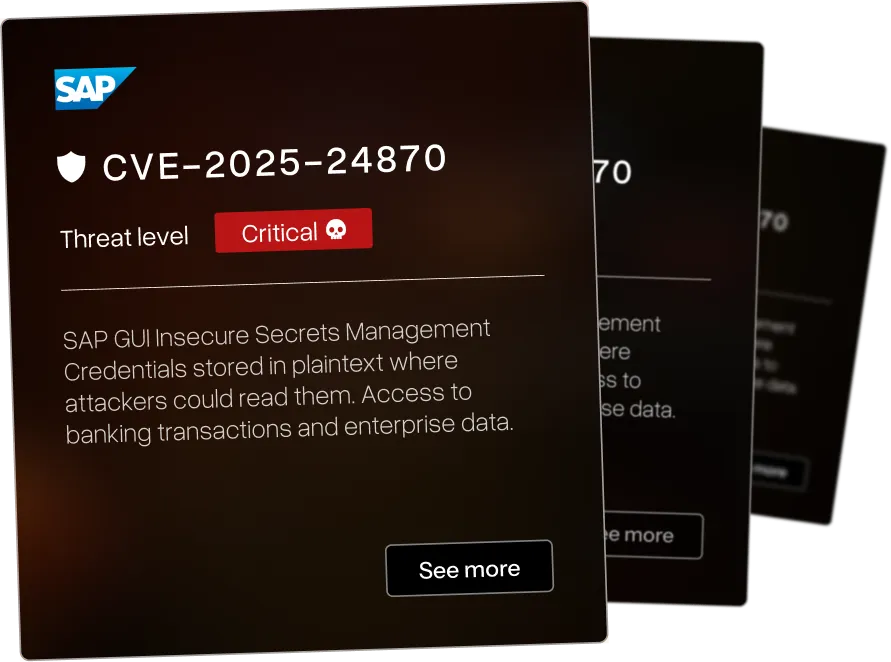
The Enterprise Security Software We Hacked
Our red team engagement operators discover vulnerabilities in the platforms healthcare organizations use We exploit both known CVEs and the vulnerabilities nobody's documented yet.


Memory corruption in Microsoft Edge (EdgeHTML) allows remote code execution via crafted web content




.webp)

Remote code execution via insecure deserialization in IBM i Access Client Solutions allows attackers to execute arbitrary code






Missing rate limiting on password change in CyberArk EPM allows brute-force attacks against user accounts




View All CVEs We've Published
.webp)


.webp)
The AFINE Adaptive Security Framework (AASF)
A framework developed from a decade of security assessments and continuously refined as attack methods evolve. Our methodology reflects current threat patterns and the practical security decisions organizations face as their attack surface expands.
We’re ready to deliver next-level security
Why Organizations Trust Us
Let's Discuss Your Security Posture
We scope every red team engagement based on your healthcare infrastructure and threat landscape. Book an assessment below to discuss your requirements.