Blog posts
Deep dives into vulnerabilities we discover, offensive security techniques we develop, and insights from the front lines of enterprise security research.
Ready_ Wasn’t Ready – Four Critical Vulnerabilities in Symfonia eDokumenty
In our latest research, we discovered four critical vulnerabilities in Symfonia eDokumenty (formerly Ready_TM), including Remote Code Execution, SQL Injection, and more. This case illustrates why consistent and thorough security testing is essential for applications handling sensitive data.
Vulnerability research
Web

Maksymilian Kubiak
February 12, 2026
5
min read
•
Jun 2, 2025

Desktop Application Testing: Essential Steps
Desktop applications handle critical business operations across enterprises. Banking software processes transactions. Healthcare apps store patient records. Manufacturing tools control production systems. They all share common security challenges that standard desktop application testing approaches miss. The problem is straightforward: most security testing methodologies were built for web and mobile applications. They don’t account for direct […]
Linux
MacOS
Vulnerability research
Windows

Paweł Woyke
February 13, 2026
3
min read
•
Nov 28, 2025
Unmasking the Security Labyrinth: Navigating the Perils of SAP GuiXT Scripting
This blog post uncovers critical vulnerabilities like Insecure Design, remote script loading, and NTLM hash theft.
SAP
Vulnerability research
Web
Windows

Michał Majchrowicz
March 23, 2026
5
min read
•
Jun 9, 2025

Null Pointer Exceptions: From Java’s Pitfalls to Kotlin’s Solutions
This article explores the root causes of NullPointerExceptions in Java and how Kotlin’s built-in null safety mechanisms offer a cleaner, safer alternative. Through practical code examples and real-world patterns, we compare both languages and highlight Kotlin’s advantages in writing more robust and maintainable code.
Web
Secure coding

Sławomir Zakrzewski
February 12, 2026
7
min read
•
Jun 16, 2025

When Memory Refuses to Forget: Sensitive Data Persistence in Desktop Application
This article explores a security flaw in desktop applications across Windows, Linux, and macOS: the persistent storage of sensitive data in memory.
Apple
Linux
MacOS
Red teaming
Secure coding

Karol Mazurek
February 12, 2026
5
min read
•
Jun 23, 2025

LLM Security: Prompt Injection Defense with CaMeL Framework
DeepMind released CaMeL, a new prompt injection security mechanism. It is based on Dual LLM design pattern. Is it an end to prompt injection?
AI
LLM

Mateusz Wojciechowski
February 12, 2026
7
min read
•
Jun 30, 2025

GraphQL Security from a Pentester’s Perspective
Discover key security vulnerabilities in GraphQL APIs, practical testing methods, and effective mitigations. Essential reading for security professionals and developers.
API
Secure coding
Vulnerability research
Web

Paweł Zdunek
February 12, 2026
32
min read
•
Jul 7, 2025

DLL Hijacking in Check Point SmartConsole installer aka CVE-2024-24916
The article provides a detailed breakdown of a DLL hijacking vulnerability in Check Point SmartConsole, explaining how malicious DLLs could be loaded to achieve remote code execution before the issue was patched.
Binary exploitation
Red teaming
Vulnerability research

Karol Mazurek
February 12, 2026
5
min read
•
Jul 21, 2025

Race Condition Vulnerability Triggers Stack Buffer Overflow in macOS
macOS kernel vulnerability where a race condition between the display reset process and frame buffer updates, causing Stack Based Buffer Overflow which leads to kernel panic (potential privilege escalation) on Apple M1 systems.
Binary exploitation
MacOS
Reverse engineering
Vulnerability research

Karol Mazurek
February 12, 2026
12
min read
•
Aug 11, 2025
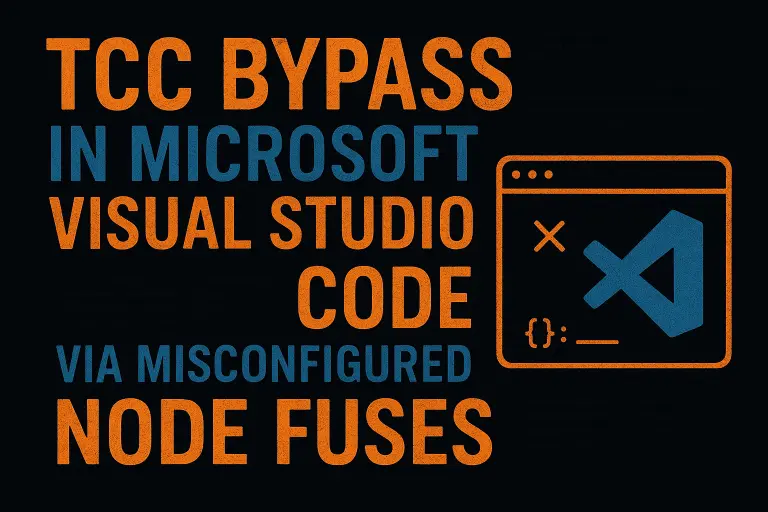
Visual Studio Code Vulnerability: macOS TCC Bypass
Microsoft Visual Studio Code on macOS has a misconfiguration in its Electron setup that enables the “RunAsNode” fuse, letting attackers bypass Apple’s TCC privacy protections and inherit sensitive permissions. It’s a proven flaw that works post-compromise, but Microsoft has refused to patch it, claiming it requires local access and doesn’t meet their servicing bar. The result is that any malware on the system could silently leverage VS Code to access private data without additional prompts.
Apple
MacOS
Red teaming
Vulnerability research

Karol Mazurek
February 27, 2026
3
min read
•
Aug 18, 2025
Sort by Categories
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
Monthly Security Report
Subscribe to our Enterprise Security Report. Every month, we share what we're discovering in enterprise software, what vulnerabilities you should watch for, and the security trends we're seeing from our offensive security work.
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
Cookie Settings
We use cookies to provide you with the best possible experience. They also allow us to analyze user behavior in order to constantly improve the website for you.
See our Privacy PolicyThank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
