NIS2 penetration testing is adversarial security testing aligned to the risk-management measures required by Article 21 of Directive (EU) 2022/2555. It's not a checkbox activity - it's the most direct way to verify whether your controls hold against a real attack.
This post covers the technical and operational layer: what Article 21 controls look like when they fail, what auditors check, and how to build an evidence chain that survives scrutiny.
What Article 21 Requires - and Where It Fails in Practice

Article 21 defines ten minimum risk-management measures that essential and important entities must implement: risk analysis, incident handling, business continuity, supply chain security, vulnerability management, effectiveness assessment, cyber hygiene, cryptography, access control, and MFA.
The critical phrase is "policies and procedures to assess the effectiveness of cybersecurity risk-management measures" - Article 21(2)(f). This is the explicit requirement for testing, not just documentation. ENISA's Technical Implementation Guidance v1.0 (June 2025) recommends penetration testing as the primary method for demonstrating effectiveness.
Commission Implementing Regulation (EU) 2024/2690 goes further. It's binding law for DNS providers, cloud computing services, data centres, MSPs, MSSPs, and other digital service categories. Its evidence standards can't be met without penetration testing.
Here's where Article 21 breaks down in practice.
Article 21(2)(a) - Risk Analysis and Security Policies
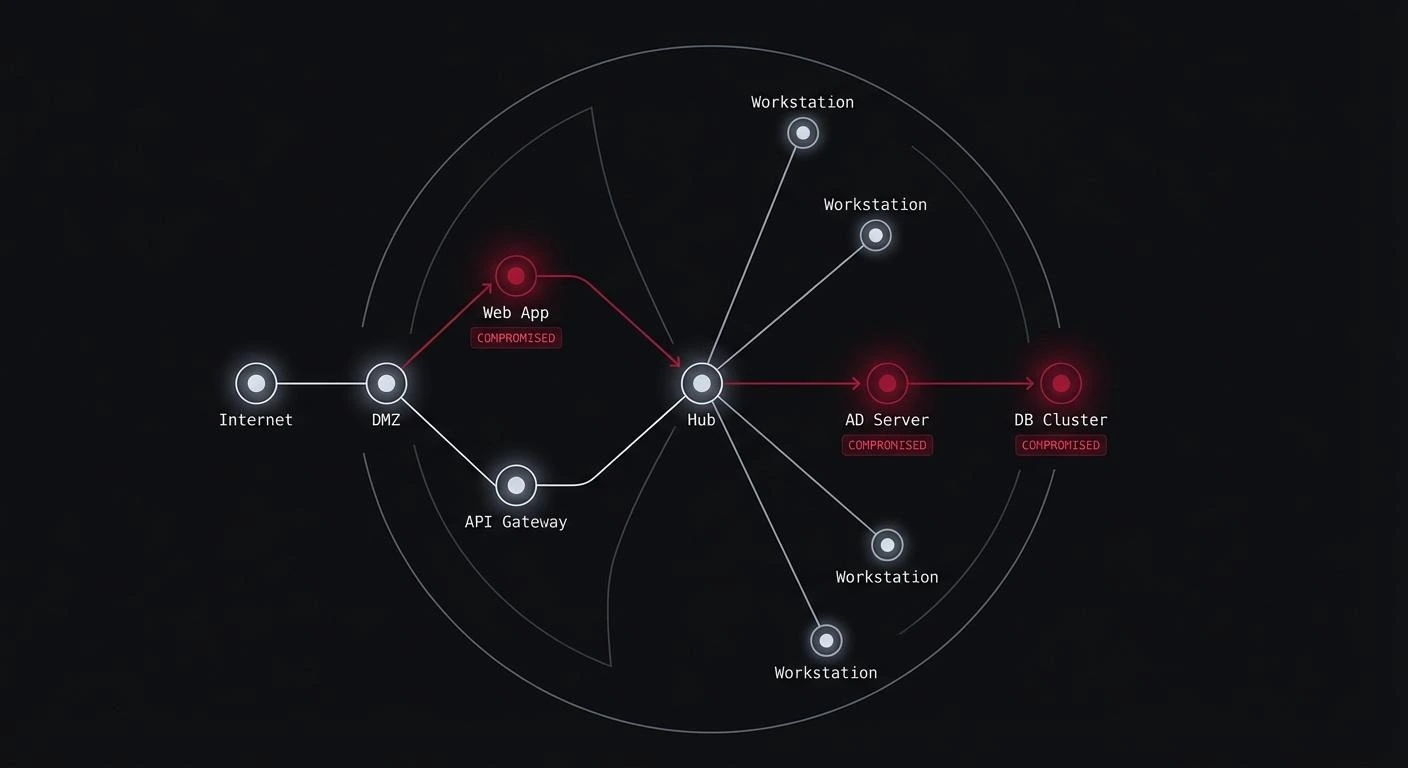
Risk registers built from interviews and questionnaires routinely miss lateral movement paths that a penetration tester finds in the first two hours. A policy stating "privileged accounts require approval" means nothing if Active Directory has 47 Domain Admin accounts that were never removed when employees left.
Article 21(2)(b) - Incident Handling
Incident response plans that have never been tested fail at the moment they're needed. During a real incident, organizations regularly discover their SIEM has no alert for the technique used, the runbook assumes network access they don't have, and nobody defined who makes the call to notify CSIRT within 24 hours as required by Article 23. Red team simulations surface this before a real incident does.
Article 21(2)(c) - Business Continuity
Backup policies are easy to document. Testing restoration under adversarial conditions - where the attacker has been present for weeks and has specifically targeted backup infrastructure - is different. This is directly relevant to the ransomware scenario NIS2 is designed to address.
Article 21(2)(d) - Supply Chain Security
Questionnaires don't find real exposure. A penetration tester looks at actual integration points: what permissions does the MSP have on the network, what does the development toolchain pull from external repositories, what vendor VPN accounts are active and unmonitored.
Article 21(2)(f) - Effectiveness Assessment
This is the explicit testing mandate. Auditors expect test reports, remediation records, retest results, and management approval of closure. A test report without a retest is an incomplete evidence chain.
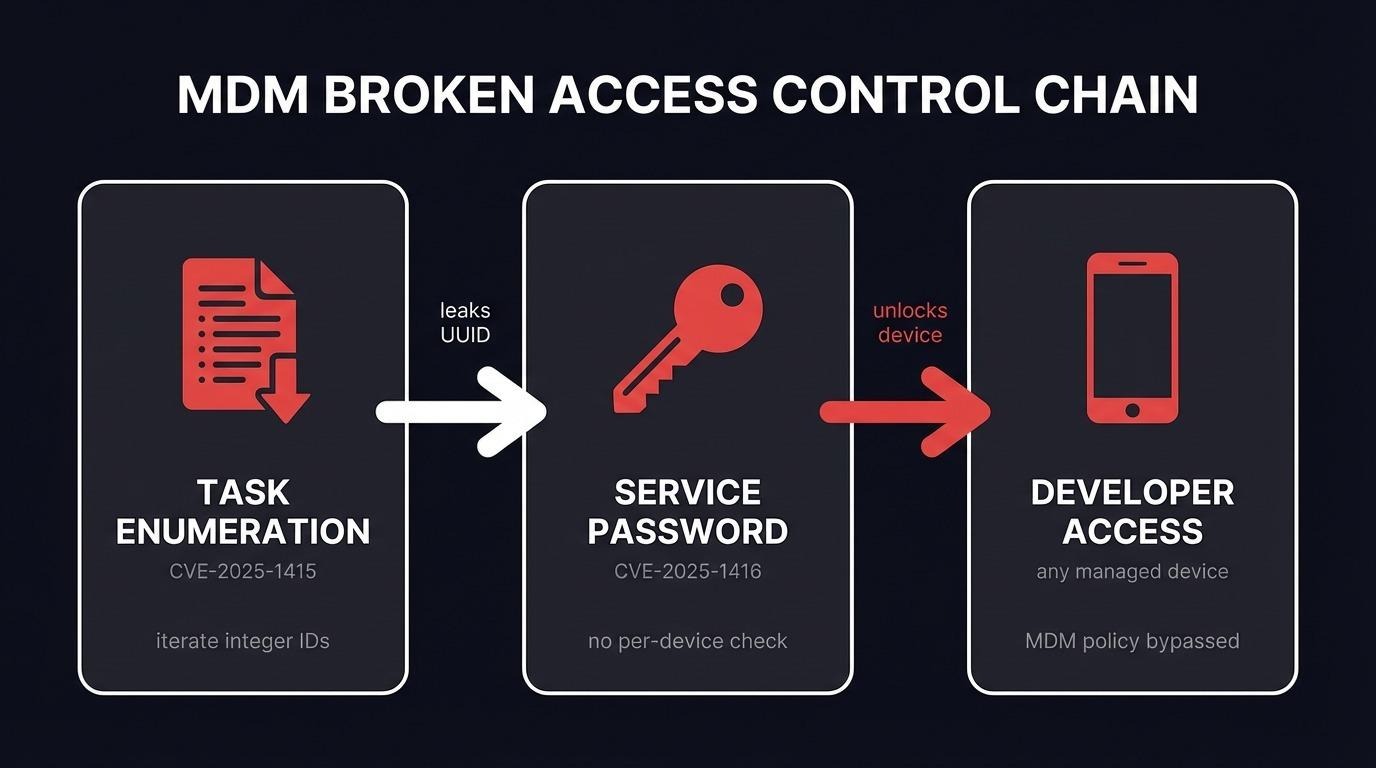
Article 21(2)(i) - Access Control and Asset Management
Most findings concentrate here. Stale service accounts with excessive permissions and Active Directory misconfigurations create the lateral movement paths that turn a phishing email into a domain compromise. MFA is a separate requirement under Article 21(2)(j) - but the access control foundation that makes MFA meaningful lives here.
Essential vs Important Entities: What the Distinction Means for Testing
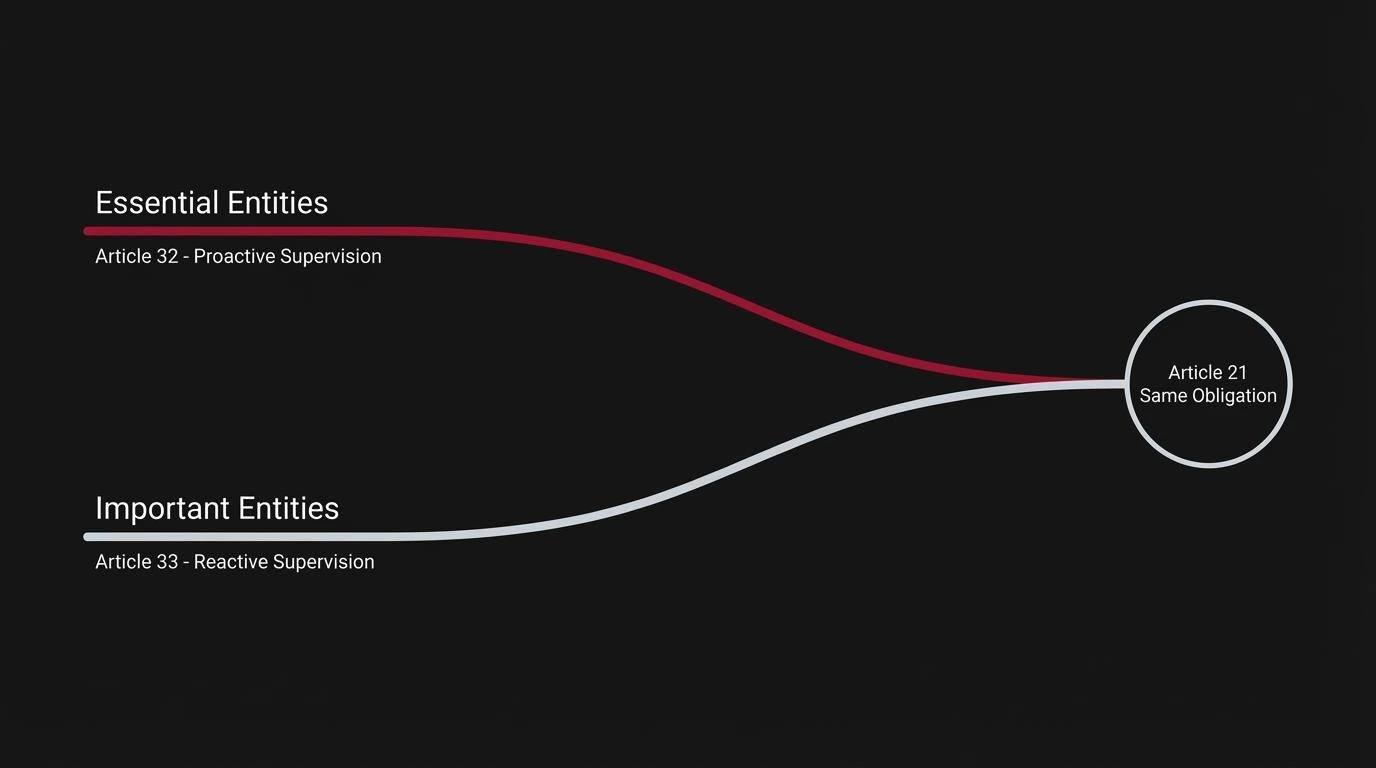
Articles 32 and 33 define two supervisory regimes with different consequences for audit timing.
Essential entities - energy, transport, banking, financial market infrastructure, health, drinking water, wastewater, digital infrastructure, and ICT service management - are subject to ex-ante supervision under Article 32. Authorities can inspect proactively, request evidence, and commission security audits without waiting for an incident. Fines reach up to 10 million euros or 2% of worldwide annual turnover, whichever is higher.
Important entities - postal services, waste management, certain manufacturing sectors, online marketplaces, and search engines - are subject to ex-post supervision under Article 33. Authorities act reactively. Fines reach up to 7 million euros or 1.4% of worldwide annual turnover.
The practical difference: essential entities need a complete, current evidence chain at all times. Important entities have more runway, but Article 21 applies equally to both. Ex-post supervision doesn't mean a lower security standard.
On frequency: ENISA guidance treats annual penetration testing as the minimum for in-scope systems, with additional testing after significant changes, after security incidents, or when threat intelligence indicates elevated sector risk. Commission Implementing Regulation (EU) 2024/2690 requires testing "on a regular basis" after significant changes. The cadence must be documented and defensible to an auditor.
The NIS2 Checklist: Mapping Article 21 Controls to What a Pentester Tests
21(2)(a) - Risk analysis and security policies
Test whether the documented threat model reflects attack paths. Common finding: the assumed kill chain isn't the actual kill chain.
21(2)(b) - Incident handling
Tabletop exercise or purple team simulation run against a realistic attack sequence. Common finding: detection gaps and unclear notification ownership. The 24-hour CSIRT early warning under Article 23 requires pre-defined decision authority.
21(2)(c) - Business continuity
Include backup system targeting in scope, run recovery tests under simulated adversarial conditions. Common finding: backup infrastructure shares the same authentication domain as production.
21(2)(d) - Supply chain security
Third-party access review, vendor account audit, testing of integration points with privileged access. Common finding: MSP accounts with excessive permissions, never reviewed since onboarding.
21(2)(e) - Vulnerability handling
External attack surface assessment and internal penetration testing. Common finding: internet-facing services running end-of-life software; internal systems with critical patches months overdue.
21(2)(f) - Effectiveness assessment
This clause mandates the testing program itself. Evidence required: scoped test reports, remediation tracking, retest results, management sign-off. This is the clause auditors follow when building their evidence request list under Article 21(2)(f).
21(2)(g) - Cyber hygiene and training
Phishing simulation, social engineering assessment, endpoint control validation. Common finding: training completion rates don't reflect real phishing resistance.
21(2)(h) - Cryptography
Cryptographic configuration assessment across web applications, APIs, internal services, and data at rest. Common finding: deprecated TLS, weak cipher suites, encryption keys stored alongside the data they protect.
21(2)(i) - Access control
Active Directory security assessment, privileged access review, identity lifecycle audit. Common findings: Domain Admin accounts provisioned for a project and never removed; kerberoastable accounts creating a direct path to domain compromise.
21(2)(j) - Multi-factor authentication
MFA coverage across authentication systems, VPN, remote access, and admin interfaces. Common finding: MFA enforced on public-facing systems but absent from internal admin interfaces and third-party VPN.
The Evidence Chain Auditors Check
Most organizations don't fail NIS2 audits at the testing stage. They fail at remediation. A test report filed and never acted on is worse than no test - it's documented evidence the organization identified a problem and chose not to fix it.
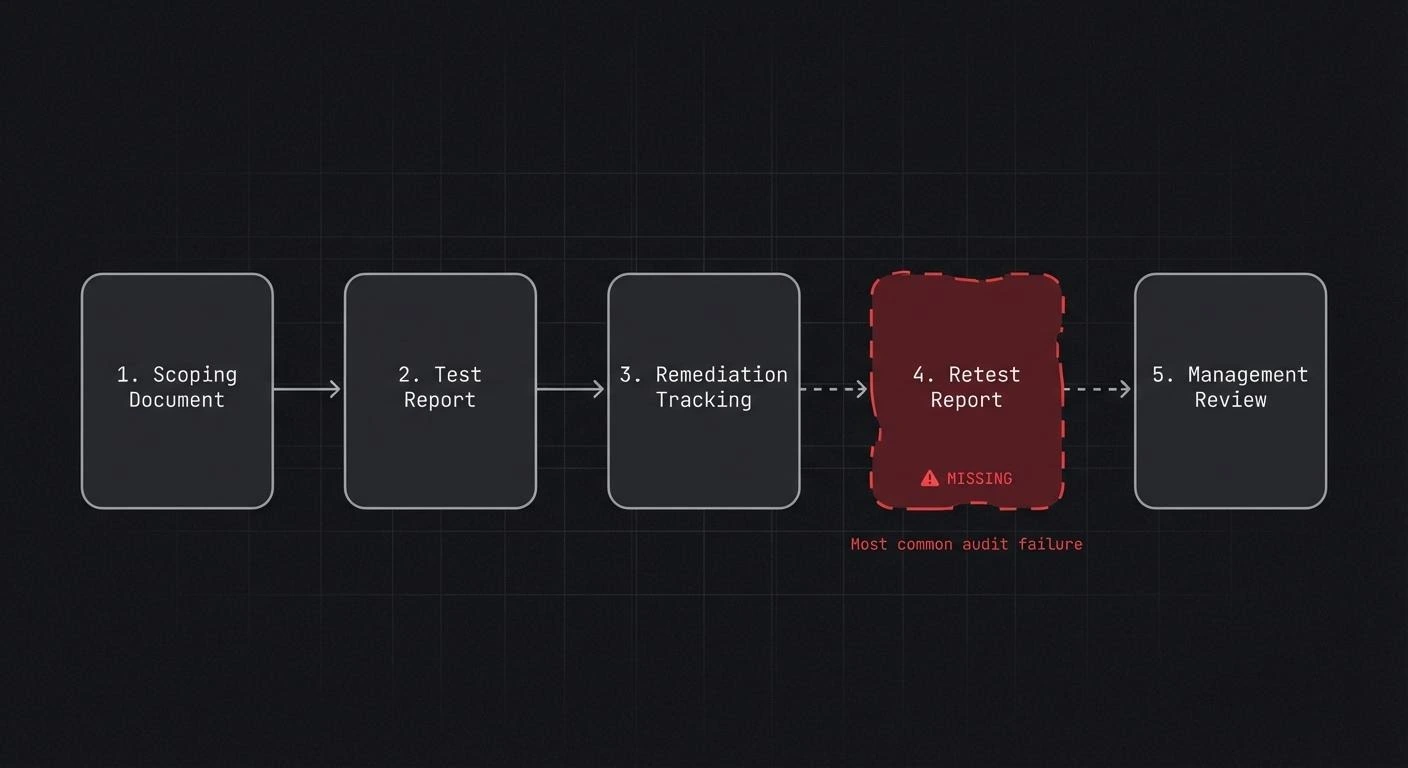
The evidence chain auditors follow under Article 21(2)(f):
1. Scoping document
Which systems, networks, and processes were in scope, tied to the asset inventory and risk register. Scope that can't be mapped to the asset inventory is a gap.
2. Test report
From an independent assessor: methodology, findings with severity ratings, reproducible proof-of-concept descriptions, and recommendations. Self-assessment doesn't satisfy Article 21(2)(f) for essential entities under proactive supervision.
3. Remediation tracking
Each finding with an assigned owner, deadline, and status. Risk acceptances need management sign-off. Findings closed as "accepted risk" without documented justification will attract scrutiny.
4. Retest report
Confirming remediations were implemented and effective. This is the most commonly missing document. Without it, an auditor can't distinguish between "we fixed it" and "we planned to fix it."
5. Management review
Evidence that findings reached and were reviewed by the management body. Article 20 requires management to approve and oversee cybersecurity risk-management measures. A testing program that never reaches management is a control failure.
Critical findings remaining open three months after report delivery are an audit problem regardless of eventual remediation.
Why Paper Compliance is the Expensive Option
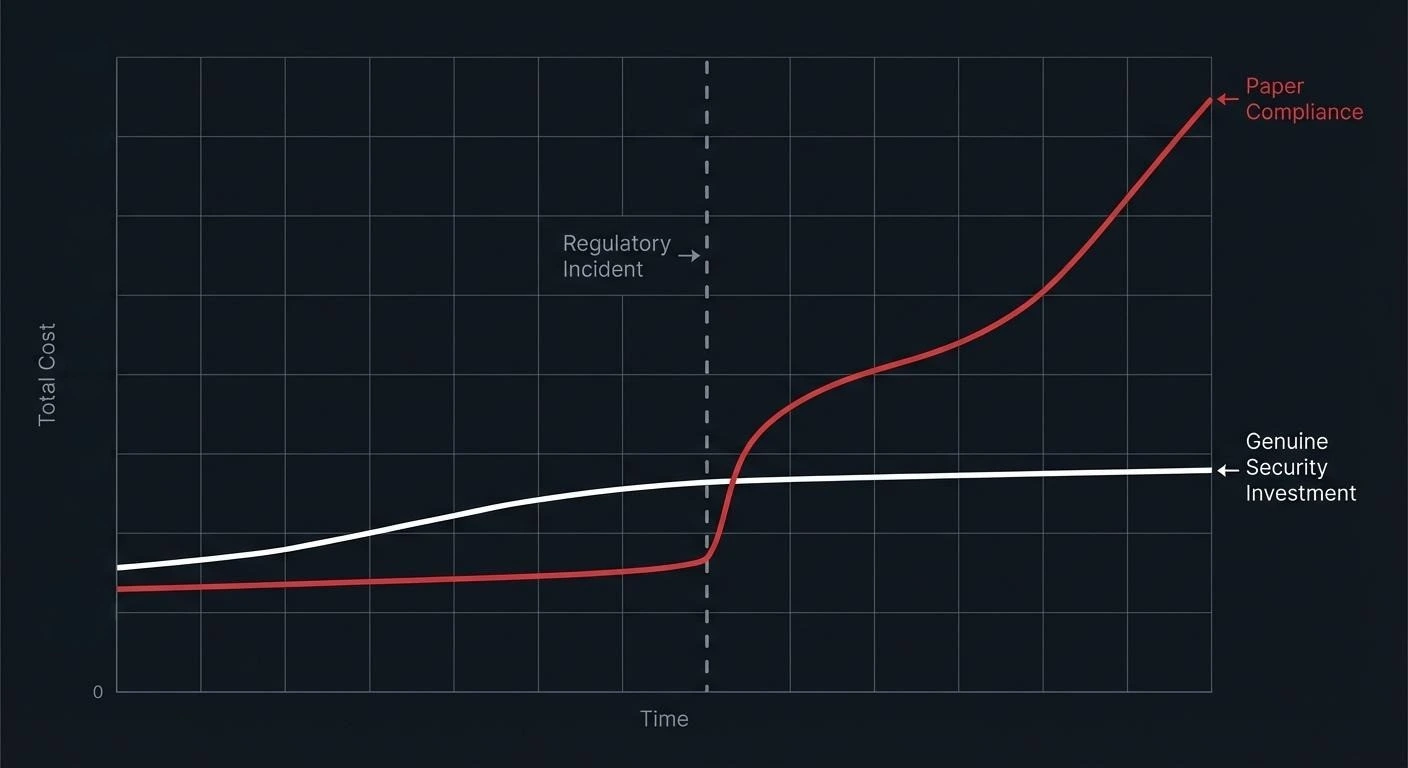
Fine exposure under Article 34 is the obvious number. For an essential entity, up to 10 million euros or 2% of worldwide annual turnover. For important entities, up to 7 million or 1.4%. These amounts are operational - competent authorities have the legal tools under Articles 32 and 33 to act.
The Article 23 notification obligation is the risk that gets less attention. A significant incident that a penetration test would have identified - and remediation would have prevented - becomes a regulatory event: 24-hour early warning, 72-hour incident notification, final report within one month. That notification triggers supervisory scrutiny of the entire security program. If the review finds unremediated findings from a prior test, the organization has documented its own negligence.
Operational disruption in NIS2-covered sectors routinely exceeds fine exposure. A ransomware event at a financial entity or healthcare provider is not a reputational inconvenience - it's a service failure with direct impact on the people those organizations serve.
A penetration test that costs 40,000 euros and produces 30 findings, 28 of which are remediated before the next audit cycle, is a better investment than an identical test treated as a document to file. The difference isn't the test - it's what happens after the report.
Implementation Sequencing: What Order Delivers Real Risk Reduction
First: external attack surface
Start with what an attacker sees from the internet. An external penetration test maps exposed attack surface, identifies exploitable weaknesses, and produces the first evidence document in the chain. This directly addresses Article 21(2)(e).
Second: identity and access
Active Directory assessments, privileged access reviews, and MFA gap analysis address Article 21(2)(i) and 21(2)(j) simultaneously. Post-breach analysis consistently finds the turning point where an attacker moved from limited access to domain administrative control in Active Directory, not in the firewall.
Third: network segmentation
Internal penetration testing mapping reachable hosts and testing segmentation between zones. Organizations that haven't tested segmentation frequently find it exists on paper but not in the network.
Fourth: incident response validation
Run a tabletop exercise against a realistic scenario for your sector: ransomware for healthcare and financial entities, supply chain compromise for digital service providers. Test the Article 23 notification process explicitly - can the organization identify a significant incident and submit the early warning within 24 hours?
Fifth: ongoing cadence
Annual penetration testing at minimum, with targeted retests after significant changes and after any security incident. ENISA frames this as a continuous process with no defined end date.
Frequently Asked Questions
What is NIS2 penetration testing and is it legally required?
NIS2 penetration testing is adversarial security testing conducted to validate the effectiveness of Article 21 risk-management measures. The directive doesn't use the term "penetration test" explicitly, but Article 21(2)(f) requires entities to assess the effectiveness of their controls. ENISA's Technical Implementation Guidance v1.0 recommends penetration testing as a primary method. For entities in scope of Commission Implementing Regulation (EU) 2024/2690, the evidence standards effectively require it. For legal interpretation specific to your jurisdiction, see olesinski.com.
How often does NIS2 require penetration testing?
Article 21 doesn't specify a frequency. The proportionality principle in Article 21(1) ties testing depth and frequency to the entity's risk exposure and size. Commission Implementing Regulation (EU) 2024/2690 requires testing "on a regular basis" and after significant changes. Industry practice, shaped by ENISA guidance, treats annual testing as the minimum for essential entities, with additional tests after architectural changes, incidents, or elevated sector threat.
What does an NIS2 audit evidence chain include?
Auditors expect five elements under Article 21(2)(f): a scoping document tied to the asset inventory; a test report from an independent assessor; a remediation tracking record with assigned owners and deadlines; a retest report confirming effective remediation; and management review documentation. The missing element in most organizations is the retest.
What is the difference between essential and important entities under NIS2?
Essential entities are subject to proactive supervision under Article 32 - authorities can inspect and audit without waiting for an incident. Important entities are subject to reactive supervision under Article 33. Both must implement the same Article 21 measures. Essential entities need a complete, current evidence chain at all times; important entities have more tolerance for gaps until a triggering event.
What are the NIS2 fines for non-compliance?
Article 34 sets minimum fine thresholds: essential entities face up to 10 million euros or 2% of worldwide annual turnover, whichever is higher. Important entities face up to 7 million euros or 1.4%. Authorities can also issue binding instructions, require public disclosure of non-compliance, and temporarily ban individuals from management roles. Member states may set higher maximums in national legislation.
Does NIS2 require an external penetration testing vendor?
Article 21 doesn't specify internal versus external testing. But the auditor interpretation of Article 21(2)(f) leans toward independent testing - conducted by a party not responsible for building or operating the systems being tested. For essential entities under proactive supervision, self-assessment is unlikely to satisfy an auditor. The practical recommendation is an external penetration testing provider with a documented, reproducible methodology.
If you need help contact AFINE.